Tufin Orchestration Suite enables organizations to reap the benefits of network change automation for the application deployment lifecycle by easily define, update, monitor and remove applications and services from the network. By providing detailed insight into an application’s connectivity needs and status, Tufin helps to accelerate service deployment, assure business continuity and simplify network operations.
Streamline Operations, Improve Collaboration.
Tufin uses automation and analytics to automate network configuration changes and to remove friction between siloed teams. It serves as a central console for all network-related application changes, ensuring that the network is always aligned with changing application requirements.
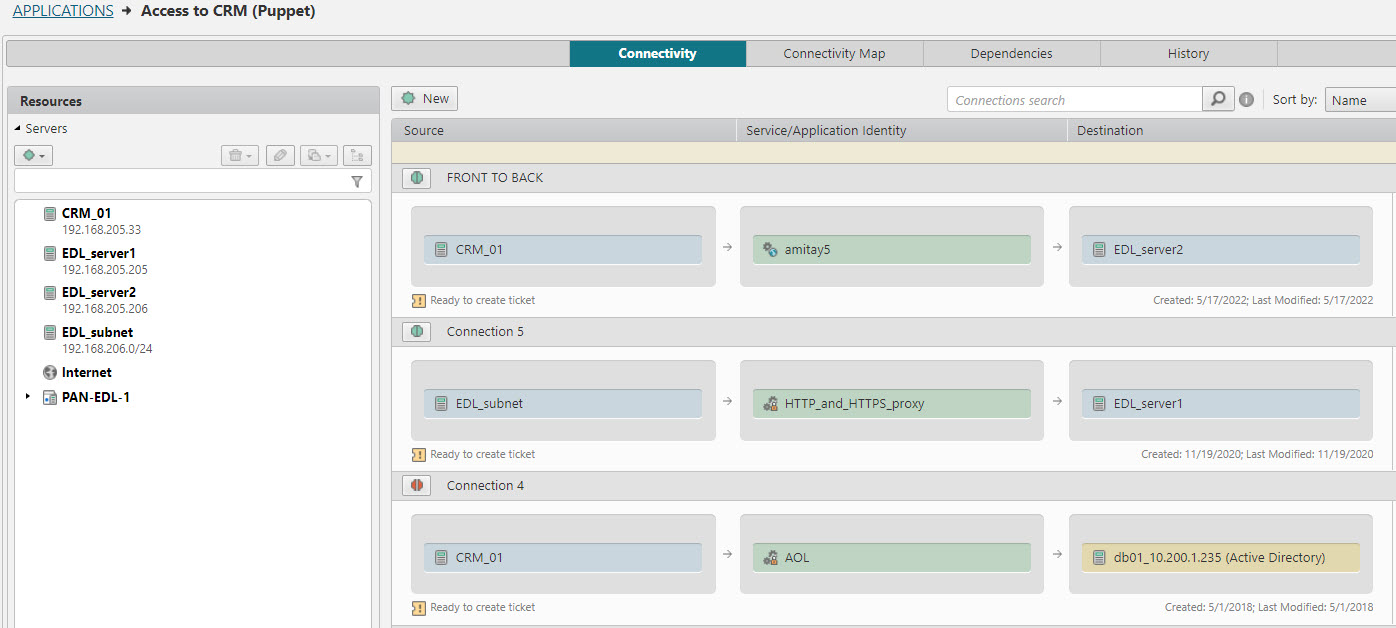
Application teams can define application components – such as web servers and databases – and the relationships between them. No understanding of the network topology is required. Once connections are defined, they can submit change tickets that automatically translate the required application changes into network access requests. At this point the network team are able to complete the design, approval, and implementation of the required network policy changes.
The Tufin Orchestration Suite dashboard always shows the applications’ connectivity status and change history to keep everyone up to date.