Attack surface management is much like planning and planting a vegetable garden. While you want your garden to grow, you need to understand the types of plants you can grow successfully, plan space for them accordingly, and respond to their needs based on your environment.
Simultaneously, you need to mitigate harm arising from invasive plants, animals, and improper drainage.
Simultaneously, you need to mitigate harm arising from invasive plants, animals, and improper drainage.
Attack surface management in your IT ecosystem is the same. You need to understand your current physical attack surface and digital environment then create appropriate boundaries to protect critical applications from cyberattacks while keeping out threat actors, identifying unnecessary firewall rules, and responding swiftly to cybersecurity incidents.
Effective network security enables you to reduce the number of potential access points, misconfigurations, and vulnerabilities that malicious actors can use to compromise sensitive data.
With Tufin, you can create a healthy digital environment by planning, defining, and implementing network segmentation for zero trust architectures that reduce the organization’s attack surface. By managing security zones more effectively and efficiently, you improve cybersecurity and compliance with:
-
Proactive capabilities, like engaging in a risk assessment before making network changes.
-
Reactive functionalities, like detecting and remediating existing violations that can lead to data breaches.
1. Set Trust Boundaries Using Security Zones for Cybersecurity
In a digital ecosystem, trust boundaries define logical data flows that enable you to set appropriate user and device access controls and permissions at various entry points. In the garden context, this looks like planting vegetables according to the amount of sun they need or their ability to support each other.
In a hybrid environment, your network likely includes diverse endpoints and technologies, such as:
-
Legacy firewalls
-
Next-generation firewalls (NGFWs)
-
Software-Defined Network controllers
-
SASE
-
Public cloud infrastructure
-
Edge devices
In a complex IT environment, ensuring that you appropriately group together critical applications and create consistent boundaries across networks and devices becomes more challenging. When different technologies use different schemas and formats, you lose visibility into network connections and data flows that can create cybersecurity gaps.
Network segmentation is a critical and complex compliance security control that focuses attack surface management. By aggregating high-risk assets to a few security zones, your team can reduce risks, like attackers using laptops, mobile devices, or IoT devices as entry points on one network segment before engaging in lateral movement to other segments.
Creating security zones reduces the physical attack surface by reducing the number of endpoints and entry points cybercriminals can exploit.
Tufin’s network segmentation capability provides vendor-agnostic rules based on predefined regulatory compliance templates so you can accelerate compliance while reducing the organization’s attack surface area. With Tufin’s Unified Security Policies (USPs), you can create standardized security policies across hybrid-cloud devices and manage them from a single interface for consistency.

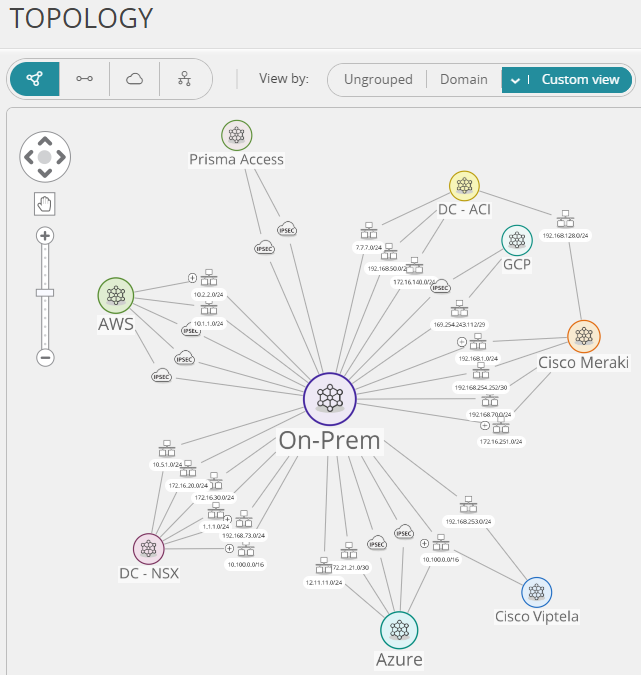
Equally important, Tufin’s network topology maps give you visibility into and across your networks. Just like you would lay out your garden with graphing paper to group plants with the same needs, these maps help you understand the different connections across your environment for visibility into critical asset groupings. This grouping can limit the impact of malware or ransomware from phishing attacks by reducing inbound and outbound traffic to high-risk endpoints, enhancing risk management.
By gaining these insights, you can engage in risk assessments that include attack vectors and potential vulnerabilities to reduce your digital attack surface more effectively and efficiently by ensuring that your security segments engage with each other as intended.
2. Cleanup Rules and Objects Regularly to Reduce Attack Vectors
Onboarding applications or other technologies often lead to rule proliferation across the organization’s network when addressing security or business requirement concerns without including the appropriate documentation.
These disabled, underutilized, or shadow rules are the invasive plants of your IT environment. As digital weeds, these rules expand your digital attack surface, reducing your networks’ health and depleting resources.
To maintain a healthy environment as your business scales, risk management processes should identify and review the need for unhealthy rules and decommission unused, shadowed, or outdated rules. This attack surface reduction method decreases the likelihood attackers can use potential vulnerabilities to gain unauthorized access.
The same way weeding a garden ensures that your critical plants have space to grow, decommissioning rules enable you to improve network and cybersecurity health by making it easier to enforce the principle of least privilege access control consistently across network devices mitigating cyber threats. Reducing the number of unnecessary rules is a critical part of any attack surface analysis.
Tufin automates policy cleanup, policy optimization, and reduces ongoing rule maintenance efforts by 85%, allowing you to allocate resources to more critical activities. Instead of spending time leaning over your keyboard to identify and remove disabled, underutilized, and shadow rules in your network environment, you can focus on more meaningful tasks, like implementing innovative security measures inside the operation.
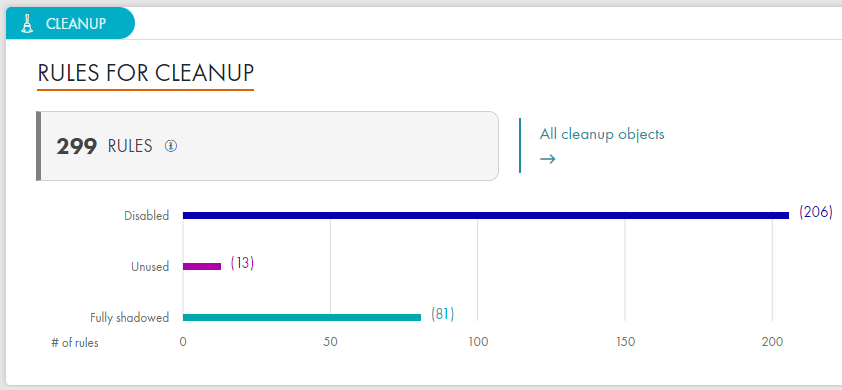
By automating the process of tracking traffic going on a rule, you can place stricter rules on that traffic to reduce the digital attack surface. To consistently enforce the principle of least privilege across network devices and more precisely, control network access, Tufin’s automatic policy generator (APG) enables you to tighten overly permissive rules that can lead to unauthorized users gaining access while reducing manual efforts.
3. Respond to Cyberattacks and incidents Faster with Accurate Network Data
In a complex network, investigating and responding to incidents is time-consuming, especially without visibility into connections across and between diverse devices. In a vegetable garden, you might try to stop bugs from eating your plants by making an insect repellent out of vinegar.
Like covering your plants with garden fabric to reduce time spent spraying repellent, attack surface reduction creates less opportunity for malicious actors to exploit potential vulnerabilities, access digital assets, or successfully spread malware and ransomware.
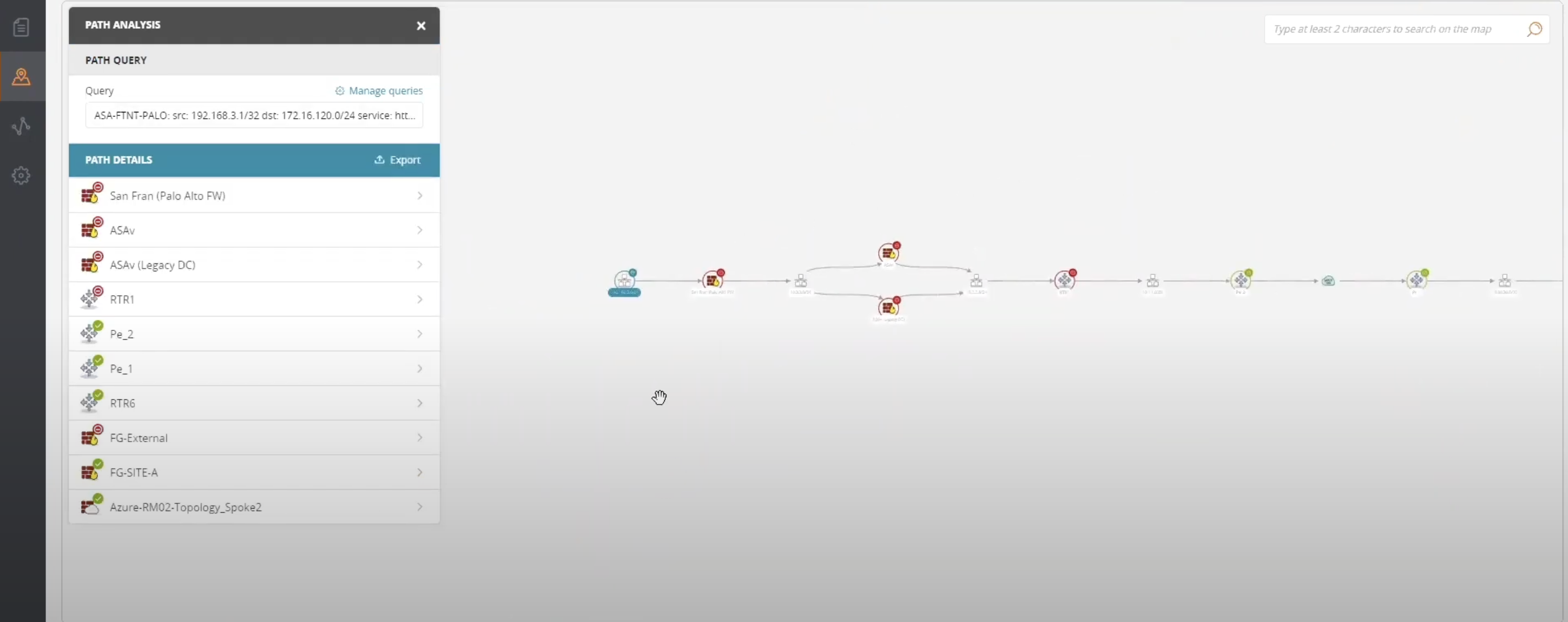
The faster you can contain a cyber threat, the more you reduce a data breach’s financial and operational impact on the organization. Tracing social engineering and cyberattacks and malware is time consuming without information about how data flows across endpoints and users. By providing immediate access to accurate firewall data, Tufin enables you to respond to cyber threats and data breaches faster, improving metrics like meant time to detect (MTTD) and mean time to respond (MTTR).
Tufin provides end-to-end network visibility in a single, shared console so network and cloud security teams can collaborate more effectively. With real-time insight into application-level traffic, you can more rapidly identify where an incident originate for critical applications, and the affected network segment by correlating data about:
-
Users whose weak passwords or accidental clicks on phishing emails may provide unauthorized access to sensitive data
-
Endpoints that might have known security vulnerabilities on unpatched software or operating systems
-
Applications that might have vulnerabilities or API misconfigurations that negatively impact security posture
These real-time insights enable network and security teams to isolate and contain the threat to digital assets more rapidly. With Tufin’s path analysis capabilities, these teams gain real-time attack surface analysis and insights to understand operational impact and prioritize remediation activities for returning critical digital assets back to their original state.
Enhanced Attack Surface Management with Tufin
Tending to a healthy IT environment takes time and effort, much like caring for a garden. While you may not be able to prevent all harm, you can mitigate risks by reducing the number of attack vectors, misconfigurations, and vulnerabilities. With Tufin, you can improve your security posture, control your digital attack surface and reduce time spent on repetitive mundane tasks, like vulnerability management, by:
-
Standardizing policies across hybrid environments
-
Enforcing security zones to protect critical applications
-
Gaining real-time visibility into and control over your network topology
-
Eliminating unhealthy rules that attackers could use to compromise networks
-
Incorporating accurate network data into incident response for faster investigations
Attack surface management with Tufin enables you to automate impactful yet manual tasks so that you can allocate resources to more strategic activities.
- Home
- Blog
- Cybersecurity
- How to Grow a Healthy Attack Surface Management Plan with Tufin










